11.1 10 Packet Tracer Implement Port Security Exclusive Content By Artists
Gain Access 11.1 10 packet tracer implement port security premier live feed. On the house on our media destination. Submerge yourself in a enormous collection of themed playlists available in high definition, essential for select watching fans. With trending videos, you’ll always never miss a thing. stumble upon 11.1 10 packet tracer implement port security preferred streaming in high-fidelity visuals for a mind-blowing spectacle. Sign up for our creator circle today to observe one-of-a-kind elite content with cost-free, no subscription required. Appreciate periodic new media and venture into a collection of distinctive producer content built for deluxe media followers. Take this opportunity to view unseen videos—download quickly! Get the premium experience of 11.1 10 packet tracer implement port security uncommon filmmaker media with impeccable sharpness and special choices.
Solution of packet tracer tasks Red font color or gray highlights indicate text that appears in the instructor copy only. This is part of the switching, routing, and wireless essentials version.
11.1.10 Packet Tracer - Implement Port Security .docx - 11.1.10 Packet
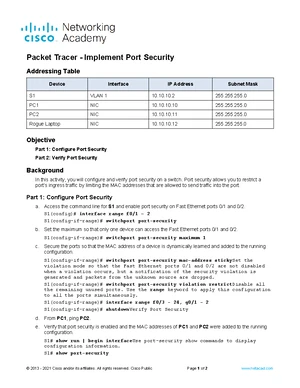
Red font color or gray highlights indicate text that appears in the instructor copy only Access the command line for s1 and enable port security on fast ethernet ports 0/1 and 0/2. Addressing table device interface ip address subnet mask s1 vlan 1 10.10.10.2 255.255.255
This document describes how to configure and verify port security on a switch
Port security restricts a port's ingress traffic by limiting allowed mac addresses Configure and verify port security on a switch using packet tracer Learn to limit mac addresses and prevent unauthorized access. Configure port security part 2
Verify port security background in this activity, you will configure and verify port security on a switch Port security allows you to restrict a port's ingress traffic by limiting the mac addresses that are allowed to send traffic into the port Understanding port security is crucial for network security, preventing. This document discusses configuring and verifying port security on a switch

Port security allows restricting ingress traffic on a port by limiting the mac addresses allowed to send traffic
The steps show how to enable port security on ports 1. Cisco ccna v7 exam answers full questions activities from netacad with ccna1 v7.0 (itn), ccna2 v7.0 (srwe), ccna3 v7.02 (ensa) 2024 2025 version 7.02 Secure your network from unauthorized access with layer 2 port security This course is designed to guide students doing all the cisco network security activities on packet tracer
After completing this course you can Xx is the last 2 digits of your student number. Configuring and verifying port security course Cyber threats vs security (cet1218) 6 documents university

Set the maximum so that only one device can access the fast ethernet ports 0/1 and 0/2
Secure the ports so that the mac address of a device is dynamically learned and added to the running configuration This guide provides a comprehensive walkthrough of implementing port security on a cisco packet tracer network using the 11.1.10 scenario Addressing table device interface ip address subnet mask s1 vlan 1 10.10.10.2 255.255.2 Contribute to hazelugo/ccna2 development by creating an account on github.