Anari.exe: Cosplay Creator Or Cybersecurity Threat? Unraveling The Digital Enigma
Hey there, fellow netizen. Have you ever stumbled upon a username that feels like a glitch in the matrix—a name that pops up in wildly different contexts, leaving you with more questions than answers? What if the same handle that brings you vibrant anime cosplay also carries a warning label from cybersecurity firms? This is the paradoxical world of anari.exe, a digital persona that straddles the line between beloved content creator and the namesake of a notorious digital threat. This article dives deep into the dual identity of anari.exe, separating the artist from the malware, and equipping you with the knowledge to navigate this complex online landscape safely.
Who is Anari.exe? The Person Behind the Pixels
Before we address the shadow, let's shine a light on the creator. The key sentences paint a picture of a vibrant, multi-platform social media personality. At its core, anari.exe is a cosplayer, online content creator, and social media personality who has built a significant following by sharing her passion for anime, gaming, and character embodiment.
Bio Data & Online Presence
| Attribute | Details |
|---|---|
| Primary Platforms | TikTok (@anariexe), Instagram, YouTube (link.me/anari.exe), Patreon, Fansly |
| Known For | Anime cosplay (e.g., Luna Snow from Marvel), JoJo's Bizarre Adventure fan content, gaming-related cosplay |
| Follower Count | ~310,000 on Instagram; 138.2k+ on TikTok; 896 subscribers on YouTube |
| Content Style | Silly, engaging short-form videos; detailed cosplay showcases; community interaction ("hello there") |
| Key Phrases | "#cosplay #fypシ゚viral #anime #marvelrivalscosplay" |
Her content is a celebration of fandom. As she states, "Hello everyone, I'm a cosplayer and also a JoJo fan." This genuine enthusiasm resonates. A standout example is her "My bunny Luna Snow cosplay ️finally got to sew some stuff myself ️" post, which highlights the hands-on, creative process behind the costumes, tagged with #marveluniverse #gamingcosplay. She actively invites her audience: "Follow me for silly cosplay videos." This approachable, creative spirit is what has garnered her a dedicated 138.2k followers on TikTok alone, who tune in for "more cosplay, fypシ゚viral, anime content."
Her business model is modern and direct. She leverages platforms like Patreon and Fansly to offer exclusive content. Phrases like "Get more from anari.exe on patreon" and "those candy cane miss fortune rewards are already available on my fansly" indicate a tiered subscription system where fans can access premium material. The mechanism is simple: "All you have to do is just sub and they will automatically appear in your dm's!" This seamless delivery is key to her creator economy.
The Other Anari.exe: Understanding the Malware Threat
Now, we pivot to the darker side of the name. The key sentences include stark warnings: "Uncover the truth behind anari.exe leaks, a notorious malware spreading across the web" and "Learn how to protect your devices and data from this malicious threat." This is not a critique of the creator, but a critical discussion about a cybersecurity hazard that has unfortunately adopted her online handle as its moniker.
What is the Anari.exe Malware?
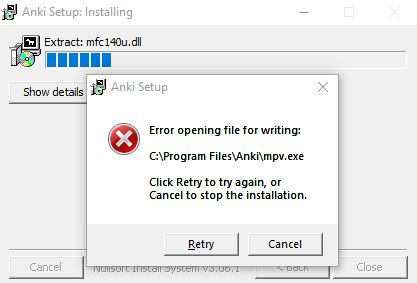
The .exe file extension is a dead giveaway—it denotes an executable file in Windows. Malware authors often use catchy, trending, or familiar names to trick users into downloading and running their malicious software. In this case, the name "anari.exe" likely leverages the popularity of the cosplayer to appear legitimate.
- Infection Vector: This malware typically spreads through phishing emails, malicious downloads disguised as game mods/cosplay resources, or compromised websites. You might see a link promising "exclusive anari.exe photosets" or "unseen cosplay videos."
- Potential Damage: While specific functionalities can vary, such malware can:
- Steal sensitive data: Passwords, banking information, cryptocurrency wallets.
- Establish backdoors: Allowing hackers remote control of your device.
- Deploy ransomware: Encrypting your files for a ransom.
- Mine cryptocurrency: Using your device's resources without consent.
- Log keystrokes: Capturing everything you type.
How to Protect Yourself: Actionable Cybersecurity Tips
The threat is real, but so are the defenses. Here is a practical checklist:
- Be Skeptical of Downloads: Never download and run an
.exefile from an unverified source, especially if promised via social media DMs or pop-up ads. Legitimate creators like the cosplayer anari.exe will never distribute content via random .exe files. - Verify Sources: Only download software or files from official websites and trusted platforms. If a "leak" or "exclusive" seems too good to be true, it is.
- Use Robust Security Software: Ensure you have a reputable antivirus/anti-malware suite installed and updated. Enable real-time scanning.
- Update Religiously: Keep your operating system, browsers, and all software patched. Updates often fix security vulnerabilities that malware exploits.
- Enable Multi-Factor Authentication (MFA): This adds a critical second layer of security to your email, social media, and financial accounts, making stolen passwords far less useful.
- Educate Yourself: Be aware of common phishing tactics. Look for misspellings in URLs, urgent language ("Act now!"), and mismatched sender addresses.
The core rule: Your favorite creator's content will be on their verified, official social channels or approved platforms like Patreon—not in a mysterious executable file.
Navigating the Content Ecosystem: Where to Find the Real Anari.exe
For fans, knowing where to find authentic content is crucial to avoid malware traps. The real anari.exe maintains a clear, verified presence:
- TikTok: Her primary short-form hub is @anariexe, where her videos—like the one with 669 likes showcasing a new cosplay—are safely viewable. She often teases content with notes like "There is more under this but tiktok won't let me show x.x" using hashtags like #nazunacosplay #callofthenight.
- YouTube: Her channel, found at link.me/anari.exe, hosts "shorts latest popular" compilations and longer looks at her work.
- Instagram: With over 310,000 followers, this is her main portfolio for high-quality cosplay photography.
- Patreon & Fansly: For exclusive, adult-oriented cosplay content, she directs subscribers to these platforms. The process is straightforward: subscribe, and content is delivered directly to your DMs or feed on the platform itself.
Always check for the verified badge (blue checkmark) and cross-reference the link in her bio. Be extremely wary of any third-party sites or Telegram channels (like those referenced in the key sentence about "sliv nude фото модели... в tg") claiming to have "leaks" or "free downloads." These are almost certainly malware distribution points or scams.
The Broader Context: Cosplay, Community, and Online Risks
The story of anari.exe is a microcosm of the modern internet. It highlights the intersection of fandom, creator economics, and pervasive cyber threats.
- The Cosplay Boom: Cosplay has exploded from niche hobby to mainstream cultural phenomenon. Platforms like TikTok and Instagram have democratized it, allowing creators like anari.exe to build careers. Hashtags like #marvelrivalscosplay show how specific game and comic releases drive content trends.
- The "Leak" Culture: Unfortunately, the popularity of creators, especially those on platforms like Fansly and OnlyFans, has spawned a dark underbelly of non-consensual content sharing ("leaks"). The key sentence referencing "Anari Exe # слив nude фото модели... в tg" points to this. It is vital to understand that accessing or sharing such leaked content is illegal, unethical, and often a vector for malware. Supporting creators through official channels is the only ethical choice.
- Digital Literacy is Non-Negotiable: This case study underscores that every internet user must develop a keen sense of digital hygiene. Your ability to distinguish a creator's official link from a malware trap is your first and best line of defense.
Conclusion: Embracing the Art, Evading the Artifice
The name anari.exe represents two distinct entities: one is a talented, human creator who pours her passion into sewing costumes, embodying characters from Luna Snow to various JoJo personas, and building a community of 138,000+ fans with her "silly cosplay videos." The other is a faceless, malicious software construct designed to exploit that very popularity for theft and destruction.
Your takeaway is clear. Celebrate the creator. Follow her on her verified channels, subscribe through official means if you wish to support her work, and engage with the vibrant cosplay community she helps foster. Simultaneously, vigorously guard against the malware. Treat all unsolicited download links with extreme suspicion, especially those piggybacking on trending names. Implement the cybersecurity practices outlined above not just for this specific threat, but as a permanent part of your digital life.
The internet's power lies in connection and creativity—the very things the real anari.exe embodies. Don't let a piece of malicious code hijack that experience. Be a smart, safe, and supportive member of the community. Stay curious about the art, and stay vigilant against the artifice.