The Fulcrum Leak: Unraveling The Star Wars Spoiler Empire And Cybersecurity Nightmares
Have you ever stumbled upon a "fulcrum leak" and wondered what it truly means? The term has surged through two very different worlds: the glittering realm of Star Wars fandom, where spoilers are currency, and the shadowy underbelly of cybersecurity, where data breaches can cripple organizations. One group, operating under the name "Fulcrum," became infamous for leaking unreleased Star Wars content, only to be silenced by legal action from Lucasfilm. Meanwhile, a similarly named entity, Fulcrumsec, has emerged as a notorious player in the ransomware and data leak landscape. This article dives deep into both phenomena, connecting the dots between entertainment leaks and digital threats, while exploring the cultural impact and practical defenses against such security risks.
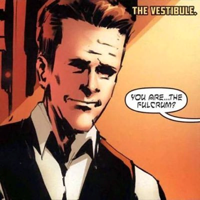
The Rise and Fall of Fulcrum: Star Wars' Most Notorious Leak Group
For years, a collective known as Fulcrum operated as a primary source for Star Wars leaks, feeding a hungry fanbase with spoilers from upcoming series and films. Their activities came to a dramatic halt when Lucasfilm, the franchise's guardian, launched a legal offensive. As reported, Fulcrum leaks was shut down after receiving "a bit of a spanking" from Lucasfilm. All their associated websites and social media accounts vanished—a clear message that intellectual property theft would not be tolerated. This group was behind major leaks, including details from Tales of the Jedi and the highly anticipated series The Acolyte. Their shutdown marked a significant victory for studios battling the relentless leak culture that thrives in the digital age.
The community that consumed these leaks is massive. The Starwarsleaks subreddit and similar platforms boast approximately 415,000 subscribers, serving as hubs for production leaks, spoilers, rumors, and news about future Star Wars media. Within this ecosystem, Fulcrum was a kingpin. Their leaks weren't just minor tidbits; they often revealed plot points, character arcs, and visual concepts that shaped fan theories months, even years, ahead of official releases. For instance, their disclosures about The Acolyte provided early insights into the series' exploration of the Sith and a new generation of Force-users.
Speaking of The Acolyte, Fulcrum's leaks painted a compelling picture of the show's narrative. Set in the final days of the High Republic era, the series follows a group known as the Acolytes. These individuals are all vying to become the apprentice of a mysterious Sith lord referred to as 'Paul'. The premise is a deadly competition where they must pick one another off until only one remains standing. Central to this story is a character named Aura. The incompetence of the Jedi in protecting her village—and their refusal to allow Aura to see her sister—becomes the catalyst for her quest. Motivated by betrayal and loss, she seeks out the Acolytes, blurring the lines between victim and perpetrator. This leaked synopsis sparked intense debate among fans about Jedi ethics and the nature of the Dark Side.
Fulcrum's operational footprint extended to social media, particularly TikTok. The account @graysaberfulcrum was a known outlet for their leaks, using short-form videos to tease images and details. This strategy capitalized on TikTok's viral nature, reaching millions beyond traditional leak forums. Their presence on such platforms underscored how leak groups adapt to new technologies to maximize impact, turning speculative fiction into trending topics overnight.
The Xqc TikTok Exposure: When a Leak Group Targets a Streamer
In a bizarre twist that blurred the lines between gaming culture and leak drama, popular streamer xQc (Félix Lengyel) found himself in Fulcrum's crosshairs. Reports surfaced that Fulcrum attempted to "expose" xQc on TikTok, likely aiming to reveal private information or past controversies. The streamer, known for his high-energy Twitch broadcasts and massive following, expressed shock over the incident. His reaction, shared across platforms, highlighted how leak groups don't just target corporations—they can weaponize information against individual content creators.
This incident occurred on a channel titled xQc Clips, which at the time had amassed 391,000 subscribers. The channel aggregates highlights from xQc's streams, but the Fulcrum attempt suggested a deeper, more malicious intent: possibly doxxing or smear campaigns. For xQc, whose career is built on public persona and real-time interaction, such an exposure posed risks to his personal safety and brand reputation. It also illustrated a growing trend where leak collectives diversify their targets beyond entertainment IP, entering the realm of influencer culture.
xQc: At a Glance
| Attribute | Details |
|---|---|
| Real Name | Félix Lengyel |
| Online Alias | xQc (formerly xQcOW) |
| Primary Platform | Twitch |
| YouTube (Clips Channel) Subscribers | 391,000 |
| Nationality | Canadian |
| Notable For | Gaming streams (Overwatch, variety), reactions, controversies, high viewer counts |
| Peak Viewership | Often exceeds 100,000 concurrent viewers on Twitch |
The Fulcrum-xQc incident serves as a cautionary tale for online personalities. Leak groups may leverage their information-gathering capabilities to target individuals, whether for extortion, notoriety, or ideological reasons. For streamers and influencers, this underscores the importance of digital hygiene: using strong, unique passwords, enabling two-factor authentication, and being wary of phishing attempts that could compromise personal data.
Fulcrumsec.net: The Dark Side of Data Leaks and Ransomware
While the Star Wars leaker Fulcrum dominated entertainment headlines, a separate entity bearing a similar name has been making waves in cybersecurity circles: Fulcrumsec. This group operates as a ransomware-as-a-service (RaaS) provider and a data leak site. In May 2024, a significant breach occurred when the domain fulcrum.pro fell victim to a data leak orchestrated by a threat actor known as Cactus. The incident, discovered on May 17, 2024, exposed an unknown volume of sensitive data, potentially including user credentials, internal communications, and proprietary information.
Fulcrumsec's primary clearnet presence is through fulcrumsec.net, which functions as a public-facing data leak site. Here, the group publishes stolen information from victim organizations, often after ransomware attacks fail to yield ransom payments. The site operates under a specific actor name—likely the alias of the hacker or group behind Fulcrumsec—which is used to brand their activities across dark web forums and leak platforms. This branding strategy helps them build a reputation in the cybercriminal underground, attracting affiliates and increasing their reach.
What makes Fulcrumsec particularly threatening is its integration with broader ransomware intelligence ecosystems. There exist open, searchable platforms that aggregate ransomware group data, providing live stats, posts, and even APIs for researchers and security teams. These tools allow defenders to monitor emerging threats like Fulcrumsec in real-time, tracking their victims, leak patterns, and technical indicators of compromise (IOCs). However, they also serve as a marketplace for cybercriminals to share tools and collaborate, lowering the barrier to entry for aspiring hackers.
The fulcrum.pro breach attributed to Cactus is a case study in how even specialized leak sites can become targets. If Fulcrumsec itself was compromised, it could mean that internal data—including affiliate lists, victim negotiations, and financial records—was exposed. This not only undermines their operations but also provides law enforcement with valuable leads. Such intra-cybercriminal conflicts are common, as rival groups or disgruntled insiders seek to sabotage or expose each other.
Protecting Against Fulcrumsec: Practical Cybersecurity Measures
Organizations and individuals must adopt proactive stances against threats like Fulcrumsec. Based on common security best practices and the specific warnings issued about this group, here are actionable steps to mitigate risk:
- Block the Domain at the Firewall and Web Proxy: Immediately restrict access to fulcrumsec.net and any associated subdomains. This can be done through firewall rule updates and web proxy filtering. Use category-based filtering to block known malicious sites, and regularly update blocklists from reputable threat intelligence sources.
- Monitor DNS Logs for Internal Clients: Implement DNS logging and monitoring to detect any internal devices attempting to resolve the Fulcrumsec domain. Unusual DNS queries can indicate malware communication or user attempts to访问 the leak site. Tools like SIEM (Security Information and Event Management) systems can correlate these events with other anomalies.
- Conduct Regular Threat Intelligence Feeds: Subscribe to feeds that track ransomware groups and data leak sites. Services offering APIs (as mentioned in sentence 11) allow automated ingestion of IOCs into security tools.
- Employee Awareness Training: Educate staff about phishing and social engineering, as these are common initial attack vectors for ransomware. Simulate phishing attacks to reinforce vigilance.
- Patch and Update Systems: Many ransomware exploits known vulnerabilities. Ensure all software, especially remote access tools and public-facing servers, is up-to-date.
- Implement Network Segmentation: Limit lateral movement by segmenting networks. If one segment is compromised, others remain protected.
- Backup Data Regularly: Maintain offline, immutable backups. In a ransomware attack, clean backups are the fastest recovery path without paying ransoms.
- Incident Response Planning: Have a tested plan for ransomware events, including communication protocols and legal considerations.
These measures form a layered defense, reducing the likelihood of a successful Fulcrumsec attack and minimizing damage if one occurs.
Fulcrum in Physical Infrastructure: Gas Leak Detection
Interestingly, the term "fulcrum" appears in a completely different context: physical infrastructure safety. A gas leak survey app is used by utility workers and inspectors to log detected leaks on gas mains, valves, and service points. This technology allows teams to track leaks, manage detection equipment, record findings, and prioritize repairs. It's a critical tool for preventing explosions, environmental damage, and service disruptions.
While this "Fulcrum" (likely a brand or software name) shares the word "leak" with its data-centric counterparts, the connection ends there. The gas leak app represents proactive, life-saving maintenance, whereas Fulcrum leaks and Fulcrumsec are reactive, malicious exploits. This juxtaposition highlights how language evolves: "fulcrum" can denote a pivotal point in mechanics, a brand in utilities, or a shadowy actor in cybercrime. For readers, it's a reminder to consider context—when you see "fulcrum leak," the meaning shifts dramatically based on the industry.
The Star Wars Leaks Community: 415k Subscribers Strong
The Starwarsleaks community, with its 415,000 subscribers, is a testament to the enduring hunger for Star Wars content beyond official channels. This subreddit and similar forums are dedicated to production leaks, spoilers, rumors, and news from future Star Wars media. Members share set photos, script excerpts, casting news, and insider tips, often sourced from groups like the now-defunct Fulcrum.
The ethics of such communities are hotly debated. Proponents argue that leaks build anticipation and hold studios accountable for secrecy that can sometimes border on over-censorship. Critics contend that leaks undermine artistic intent, spoil fan experiences, and can impact box office performance and merchandise sales. The shutdown of Fulcrum by Lucasfilm was a direct response to these concerns, signaling that studios will pursue legal avenues to protect their creations.
For fans, navigating leak communities requires discernment. Not all leaks are accurate; some are fabrications or misinterpretations. Reliable sources often have a track record of verified disclosures. However, even accurate leaks can alter the creative landscape, forcing studios to adjust marketing strategies or even rewrite scenes if major plot points surface prematurely. The dynamic between leakers, fans, and corporations is a perpetual game of cat and mouse, with each side evolving tactics.
Conclusion: The Dual Legacy of Fulcrum Leaks
The story of "fulcrum leak" is a tale of two worlds. In entertainment, the Fulcrum leak group represented the pinnacle of Star Wars spoiler culture, ultimately brought down by Lucasfilm's legal might. Their leaks about The Acolyte and other projects fueled fan speculation but also sparked discussions about the boundaries of fan engagement versus corporate control. The incident involving xQc showed how these groups could extend their reach into personal attacks on influencers, adding a new layer of risk for online personalities.
In cybersecurity, Fulcrumsec.net stands as a persistent threat, embodying the ransomware economy that targets organizations worldwide. The data leak on fulcrum.pro by Cactus is a reminder that even cybercriminals are not immune to breaches. Defending against such actors requires vigilance: blocking malicious domains, monitoring DNS logs, and staying informed through ransomware intelligence platforms.
Meanwhile, the unrelated gas leak survey app serves as a linguistic footnote, reminding us that "fulcrum" and "leak" can mean very different things in different contexts. Yet, the underlying theme is control—whether it's controlling narrative spoilers, controlling data through extortion, or controlling physical infrastructure to prevent disasters.
As we move forward, the lessons are clear. For Star Wars fans, the era of Fulcrum may be over, but leak communities will persist, adapting to new security measures. For cybersecurity professionals, groups like Fulcrumsec demand continuous adaptation in defense strategies. And for all of us, understanding these diverse "fulcrum leaks" helps us navigate a world where information—whether about galaxy-spanning sagas or our personal data—is both a powerful asset and a potential vulnerability. Stay informed, stay secure, and may the Force be with your digital defenses.