Telegram Leaks: 200+ Million User Records Exposed – What You Need To Know
Are your private messages, phone number, and email truly safe on Telegram? The promise of secure, private messaging is a core feature of platforms like Telegram, but a relentless wave of telegram leaks has shattered that illusion for hundreds of millions. A series of massive data breaches has seen staggering volumes of user information—including email addresses, phone numbers, and usernames—dumped on criminal forums, fueling phishing epidemics and identity theft. This isn't a hypothetical threat; it's an active, escalating crisis where telegram channels have become the black markets of stolen data. This comprehensive guide dissects the latest telegram leaks, explains how your data ends up there, and provides the essential, actionable steps you must take to safeguard your privacy in an era where your digital footprint is constantly under siege.
The Scale of the Crisis: Understanding the Major Telegram Data Breaches
The sheer volume of data compromised in recent telegram leaks is almost incomprehensible. It's not a single event but a persistent pattern of massive data exposures that have accumulated over time.
The 200 Million Record Breach: A Foundational Catastrophe
The first alarm bell was deafening. Over 200 million Telegram user records, including emails and phone numbers, have been shared on a data leak forum, raising fears of massive phishing campaigns. This major Telegram data breach put a colossal portion of the platform's user base at direct risk. Attackers posted the stolen data—a treasure trove of email addresses, phone numbers, usernames, and names—on a popular leak forum, instantly making it available to any cybercriminal worldwide. The exposed information is a perfect recipe for highly targeted phishing attacks (where scammers impersonate legitimate entities to steal credentials) and smishing (SMS phishing) via the leaked phone numbers.
The HIBP (Have I Been Pwned) Confirmations: Independent Verification
The validity and scale of these breaches were independently confirmed by the gold standard in breach tracking, Troy Hunt's Have I Been Pwned (HIBP) service. The latest Telegram leaks have exposed over 361 million email addresses linked to active Telegram accounts, according to data from Have I Been Pwned (HIBP). This dataset is separate from the initial 200 million and highlights how multiple, distinct breaches have compounded the problem.
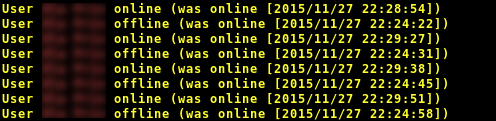
Furthermore, HIBP has added over 284 million compromised accounts harvested from stealer malware and leaked on Telegram. This points to a different, equally dangerous vector: info-stealer malware. In July 2024, info-stealer logs with 26 million unique email addresses were collated from malicious Telegram channels. The data contained 22GB of logs consisting of email addresses, passwords, and the websites they were used on, all obtained by malware running on infected machines. This isn't just a Telegram platform breach; it's data stolen from users' own computers via malware, then aggregated and sold via Telegram channels.
The Alien Textbase Channel: A 1.5TB Treasure Trove
One of the most staggering discoveries was a massive 1.5TB trove of logs from the Alien Textbase channel. This dataset, discovered in a massive 1.5TB trove of logs from the Alien Textbase channel, underscores the growing role of messaging platforms in cybercrime. According to HIBP founder Troy Hunt, the breach contained billions of rows of compromised credentials and personal data, all shared openly within a Telegram channel dedicated to such leaks. These Telegram leaks originated from more than 1,700 compromised files circulating within such ecosystems.
Why Telegram? The Platform's Dark Side as a Cybercrime Hub
Telegram had more than 200 million user records purportedly obtained from a trio of databases exposed in breachforums on Jan. But why is Telegram the platform of choice for these leaks? The answer lies in its very design features, which cybercriminals have expertly weaponized.
Anonymity, Access, and Speed: The Criminal's Toolkit
In recent years, Telegram has become one of the main platforms used by cybercriminals for the distribution of stolen credentials.Thanks to easy access, guaranteed anonymity, and the ability to share files quickly, numerous Telegram groups and channels have flourished as illicit marketplaces. Unlike more regulated platforms, creating a channel is simple, and administrators can operate with a significant degree of anonymity. The ability to share enormous files (like the 1.5TB trove) and massive lists of emails in seconds makes it the perfect distribution network for telegram leaks.
The "Pyt Telegram Teen" Phenomenon and Beyond
The platform's structure also fosters niche criminal communities. The phrase 'pyt telegram teen' specifically points to communities on this platform where 'pyt,' often an abbreviation for 'pretty young thing,' is combined with 'teen.' This is a grim indicator of how Telegram channels are used to traffic and share exploitative material, demonstrating the breadth of illicit activity enabled by the app's loose moderation in certain areas.
The Real-World Risks: From Phishing to Identity Theft
What happens when your data is in a telegram leak? The consequences are severe and personal.
- Hyper-Targeted Phishing & Smishing: With your email and phone number, attackers can craft incredibly convincing messages. They might text you a link posing as your bank (using your phone number) or email you a "security alert" from a service you use (using your email). The goal is to trick you into entering your password on a fake site.
- Credential Stuffing Attacks: If your password was included in a stealer log (email addresses, passwords and the websites they were used on), criminals will automatically try that same password on hundreds of other popular sites (Gmail, Facebook, Netflix, your bank). This works because many people reuse passwords.
- Identity Theft & Account Takeover: With enough personal data (name, email, phone), a criminal can attempt to reset passwords on your accounts, impersonate you to customer service, or open new lines of credit in your name.
- Doxxing and Harassment: Public exposure of your phone number or personal details can lead to real-world stalking, harassment, or swatting (making a false report to police to send a SWAT team to your home).
- Erosion of Trust: The Telegram leaks fundamentally undermine trust in digital communication. Users who chose Telegram for its privacy promises feel betrayed, and the incident fuels a general sense of digital vulnerability.
Proactive Protection: Your Action Plan Against Telegram Leaks
Safeguard your privacy, prevent data misuse and stay secure online. While you cannot remove your data from a telegram leak once it's public, you can dramatically reduce the damage. This article has been updated to reflect the current status, activity, and reliability of Telegram channels associated with credential leaks, and so must your security habits.
Immediate Damage Control Steps
- Check Have I Been Pwned: Go to haveibeenpwned.com and enter your email addresses and phone numbers. This will tell you which breaches your data appeared in, including the Telegram leaks. {{meta_keyword}}
- Change Critical Passwords NOW: Immediately change passwords for your email account, banking apps, and social media. Do not just change them; create strong, unique passwords for every single account. A password manager (like Bitwarden, 1Password, or KeePass) is essential for generating and storing these.
- Enable Two-Factor Authentication (2FA) Everywhere: This is your single most important defense. Even if a password is leaked, a criminal cannot log in without the second factor (a code from an authenticator app like Google Authenticator or Authy, or a hardware key). Enable 2FA on your email first, as that is the key to resetting all other passwords.
- Beware of Phishing Attempts: Assume any unsolicited email or text (especially those referencing the Telegram leaks or "security alerts") is malicious. Never click links or download attachments from unknown senders. Go directly to the official website or app by typing the address yourself.
- Monitor Your Accounts: Set up alerts for login attempts on your email and financial accounts. Review account activity logs regularly for unfamiliar locations or devices.
Long-Term Security Hygiene
- Use a Separate Email for Important Accounts: Consider using a dedicated, highly secure email address (with a strong, unique password and 2FA) for banking, primary email, and password resets. Use a separate, less important email for newsletters and forum sign-ups.
- Assume Your Data is Out There: The massive Telegram leaks mean your email and possibly phone number are in the wild. Adopt a mindset of zero trust for unsolicited communications.
- Review App Permissions: Regularly check what third-party apps have access to your Telegram account (via Telegram's Settings > Privacy and Security > Active Sessions) and revoke any you don't recognize.
- Keep Software Updated: Ensure your operating system, browser, and especially antivirus/anti-malware software are always up-to-date to protect against info-stealer malware that harvests data from your device.
The Evolving Threat: From Data Leaks to "Snap Leaks" and Beyond
The rise of snap leaks on Telegram the phenomenon of snap leaks on Telegram can be attributed to several factors. The same infrastructure that distributes credential dumps also facilitates the sharing of other non-consensual intimate imagery (often referred to as "revenge porn" or "image-based abuse"). Firstly, Telegram's emphasis on anonymity and privacy has created an environment where users feel more comfortable sharing content without fear of repercussions. This same shield of anonymity protects those who share stolen or private content.
Massive telegram leaks rock the messaging platform Linkwatcher has identified a critical security event affecting millions of users worldwide. The term "telegram leaks" now encompasses a vast ecosystem of criminal activity: from the initial data breach or malware infection, to the aggregation of stealer logs, to the final distribution on telegram channels like the infamous Alien Textbase. In yet another sign of cybercriminals shifting their tactics, they are not just hacking platforms; they are using the platforms themselves as the distribution layer for the data they steal via other means.
New content added daily & with zero subscription fees on our premium viewing center. View 1.2k onlybox telegram channel telegram nsfw onlyfans leaks | 15 leaks each 12 hours. Sentences like these, often found in search results related to telegram leaks, highlight the commercial and disturbing nature of these channels. They are not just repositories of credentials but also marketplaces for stolen private content, demonstrating the platform's dual-use problem.
Watch short videos about telegram leak investigation 2025 from people around the world. See it instantly deluxe teen leaks telegram with superb clarity ready to play. The promotional language used for these illegal channels mirrors legitimate content marketing, showing how normalized this activity has become within certain corners of the app.
Conclusion: Vigilance is the New Normal
The era of assuming your data is safe because you use a "private" messaging app is over. The cascade of telegram leaks—from the 200+ million user record breaches to the 1.5TB stealer log dumps—proves that your personal information is a commodity traded on shadowy Telegram channels. Telegram channels, telegram leaks, telegram channel and more are not just search terms; they are gateways to a thriving underground economy built on your compromised data.
The platform's architecture of anonymity and ease of file sharing, while valuable for legitimate privacy needs, has been catastrophically exploited by cybercriminals. The phrase pyt telegram teen is a chilling example of how these features enable the worst kinds of content and data trafficking.
Your protection no longer depends on the security of a single platform. It depends on your personal security stack: unique passwords, universal 2FA, vigilant phishing detection, and routine checks on breach notification sites like HIBP. The Telegram leaks are a watershed moment. They are a permanent stain on the platform's reputation and a permanent risk in your digital life. The only way forward is to operate under the assumption that your email and phone number are already public, and to build your digital defenses accordingly. Stay informed, stay proactive, and never click that suspicious link. Your online security is in your hands.