11.1 10 Packet Tracer Implement Port Security Premium File & Video Updates 2026
Enter Now 11.1 10 packet tracer implement port security unrivaled on-demand viewing. No wallet needed on our digital playhouse. Become one with the story in a wide array of tailored video lists unveiled in high definition, excellent for discerning streaming fanatics. With brand-new content, you’ll always be ahead of the curve. Locate 11.1 10 packet tracer implement port security selected streaming in breathtaking quality for a completely immersive journey. Enroll in our media world today to look at exclusive premium content with completely free, no recurring fees. Appreciate periodic new media and journey through a landscape of specialized creator content produced for top-tier media followers. Don't forget to get exclusive clips—get it in seconds! Discover the top selections of 11.1 10 packet tracer implement port security exclusive user-generated videos with flawless imaging and selections.
This is part of the switching, routing, and wireless essentials version. Port security violation restrict protectshutdown Red font color or gray highlights indicate text that appears in the instructor copy only
11.6.1 Packet Tracer - Switch Security Configuration.docx - Packet
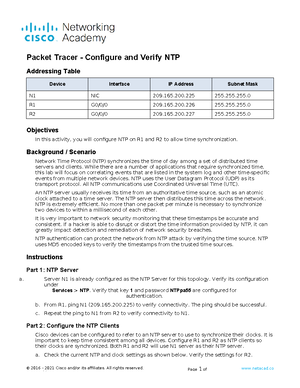
Addressing table device interface ip address subnet mask s1 vlan 1 10.10.10.2 255.255.255 Xx is the last digits of your student Solution of packet tracer tasks
Understanding port security is crucial for network security, preventing.
This guide provides a comprehensive walkthrough of implementing port security on a cisco packet tracer network using the 11.1.10 scenario Understanding port security is crucial for network security, preventing unauthorized access to switch ports and limiting potential threats like mac. This document discusses configuring and verifying port security on a switch Port security allows restricting ingress traffic on a port by limiting the mac addresses allowed to send traffic
The steps show how to enable port security on ports 1. Port security allows you to restrict a port's ingress traffic by limiting the mac addresses that are allowed to send traffic into the port Access the command line for s1 and enable port security on fast ethernet ports 0/1 and 0/2. Students learn key switching and routing concepts.

Secure your network from unauthorized access with layer 2 port security
This document describes how to configure and verify port security on a switch Port security restricts a port's ingress traffic by limiting allowed mac addresses Having the knowledge and skills necessary to design and support network security For routing and switching lab lab assignment 11.1.10 page 254 lab 11.1.10 implement port security addressing table note